How to Master Vulnerability assessment for new AI en…
VIII. Concluding Reflections on Future Trajectories and Personal Engagement Ultimately, looking past the quarterly reports and the political skirmishes reveals …
VIII. Concluding Reflections on Future Trajectories and Personal Engagement Ultimately, looking past the quarterly reports and the political skirmishes reveals …
OpenAI Adds New Teen Safety Rules to ChatGPT as Lawmakers Weigh AI Standards for Minors
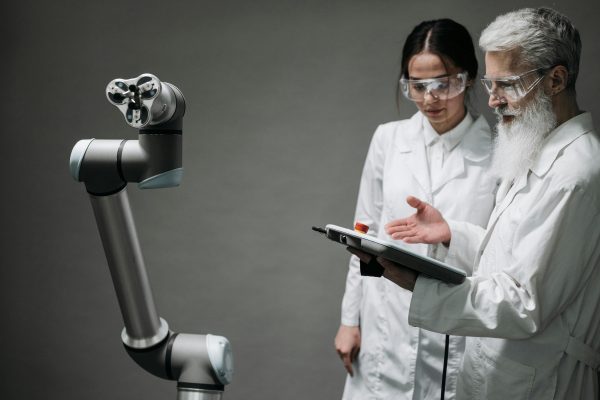
The rapidly evolving landscape of generative Artificial Intelligence, …

The Strategic Shift: Dependency Resilience Over Vendor Trust The foundational concept driving resilience engineering in 2025 and beyond is recognizing the limit…
The Long-Term View: A Race, Not an Upset The bottom line as this transformative year concludes is this: the two early catalysts—the hardware fabric provider and…

Contextualizing Wealth: Precursor Events That Built the Momentum The Supreme Court ruling was the final, explosive catalyst, but the ground was prepared months …

The Enduring Influence of Major Technology Conglomerate Backing If the technology is the engine, the backing from China’s two largest technology titans—Alibaba …
Discover how Turo can transform your travel experience! Unlock hidden gems, save money, and unleash your adventure spirit today! Image courtesy of teras dondon via Pexels Table of Contents Understanding the Turo Car Rental Concept How to Book Your Car through Turo Navigating the Common Roadblocks Enhance Your Renting Experience with ChatGPT Why Choose Turo…

Conclusion: The New Rules of the AI Economy The financial realities underpinning today’s AI giants are stark, unforgiving, and centered entirely on physical inf…

The Chilling Signal: Insurance Industry Unease Over AI Liability The localized issue of mortgage screening errors and their insurance coverage ripples outward, …

New Vectors for Misuse and the Escalation of Societal Scrutiny The dual-use nature of this powerful generative technology ensures that every technological leap …